Proprietary software

Proprietary software
Proprietary software, also known as closed-source software, is a non-free computer software for which the software's publisher or another person retains intellectual property rights—usually copyright of the source code,[1] but sometimes patent rights.[2]
Origin
Until the late 1960s computers—large and expensive mainframe computers, machines in specially air-conditioned computer rooms—were leased to customers rather than sold.[3][4] Service and all software available were usually supplied by manufacturers without separate charge until 1969. Computer vendors usually provided the source code for installed software to customers. Customers who developed software often made it available to others without charge.[5] Closed source means computer programs whose source code is not published. It is available to be edited only by the organization that developed it.
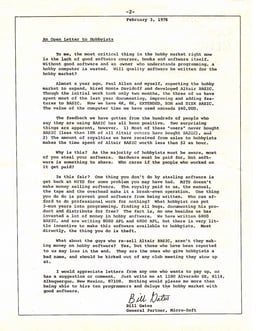
Bill Gates' "Open Letter to Hobbyists" in 1976 decried computer hobbyists' rampant copyright infringement of software, particularly Microsoft's Altair BASIC interpreter, and reminded his audience that their theft from programmers hindered his ability to produce quality software.[9]
According to Brewster Kahle the legal characteristic of software changed also due to the U.S. Copyright Act of 1976.[10]
In 1983, binary software became copyrightable in the United States as well by the Apple vs. Franklin law decision,[13] before which only source code was copyrightable.[14] Additionally, the growing availability of millions of computers based on the same microprocessor architecture created for the first time an unfragmented and big enough market for binary distributed software.[14]
Legal basis
Most of the software is covered by copyright which, along with contract law, patents, and trade secrets, provides legal basis for its owner to establish exclusive rights.[15]
A software vendor delineates the specific terms of use in an end-user license agreement (EULA). The user may agree to this contract in writing, interactively on screen (clickwrap), or by opening the box containing the software (shrink wrap licensing). License agreements are usually not negotiable.[16] Software patents grant exclusive rights to algorithms, software features, or other patentable subject matter, with coverage varying by jurisdiction. Vendors sometimes grant patent rights to the user in the license agreement.[17] The source code for a piece of software is routinely handled as a trade secret.[18] Occasionally, software is made available with fewer restrictions on licensing or source-code access; such software is known as "free" or "open-source."[19]
Limitations
Since license agreements do not override applicable copyright law or contract law, provisions in conflict with applicable law are not enforceable.[20] Some software is specifically licensed and not sold, in order to avoid limitations of copyright such as the first-sale doctrine.[21]
Exclusive rights
The owner of proprietary software exercises certain exclusive rights over the software. The owner can restrict use, inspection of source code, modification of source code, and redistribution.
Use of the software
Vendors typically limit the number of computers on which software can be used, and prohibit the user from installing the software on extra computers. Restricted use is sometimes enforced through a technical measure, such as product activation, a product key or serial number, a hardware key, or copy protection.
Vendors may also distribute versions that remove particular features, or versions which allow only certain fields of endeavor, such as non-commercial, educational, or non-profit use.
Use restrictions vary by license:
Windows Vista Starter is restricted to running a maximum of three concurrent applications.
The retail edition of Microsoft Office Home and Student 2007 is limited to non-commercial use on up to three devices in one household.
Windows XP can be installed on one computer, and limits the number of network file sharing connections to 10.[22] The Home Edition disables features present in Windows XP Professional.
Traditionally, Adobe licenses are limited to one user, but allow the user to install a second copy on a home computer or laptop.[23] This is no longer true with the switching to Creative Cloud.
iWork '09, Apple's productivity suite, is available in a five-user family pack, for use on up to five computers in a household.[24]
Inspection and modification of source code
Vendors typically distribute proprietary software in compiled form, usually the machine language understood by the computer's central processing unit. They typically retain the source code, or human-readable version of the software, written in a higher level programming language.[25] This scheme is often referred to as closed source.[26]
While most proprietary software is distributed without the source code, some vendors distribute the source code or otherwise make it available to customers. For example, users who have purchased a license for the Internet forum software vBulletin can modify the source for their own site but cannot redistribute it. This is true for many web applications, which must be in source code form when being run by a web server. The source code is covered by a non-disclosure agreement or a license that allows, for example, study and modification, but not redistribution. The text-based email client Pine and certain implementations of Secure Shell are distributed with proprietary licenses that make the source code available.
Some governments fear that proprietary software may include defects or malicious features which would compromise sensitive information. In 2003 Microsoft established a Government Security Program (GSP) to allow governments to view source code and Microsoft security documentation, of which the Chinese government was an early participant.[27][28] The program is part of Microsoft's broader Shared Source Initiative which provides source code access for some products. The Reference Source License (Ms-RSL) and Limited Public License (Ms-LPL) are proprietary software licenses where the source code is made available.
Software vendors sometimes use obfuscated code to impede users who would reverse engineer the software. This is particularly common with certain programming languages. For example, the bytecode for programs written in Java can be easily decompiled to somewhat usable code, and the source code for programs written in scripting languages such as PHP or JavaScript is available at run time.[31]
Redistribution
Proprietary software vendors can prohibit the users from sharing the software with others. Another unique license is required for another party to use the software.
In the case of proprietary software with source code available, the vendor may also prohibit customers from distributing their modifications to the source code.
Shareware is closed-source software whose owner encourages redistribution at no cost, but which the user sometimes must pay to use after a trial period. The fee usually allows use by a single user or computer. In some cases, software features are restricted during or after the trial period, a practice sometimes called crippleware.
Interoperability with software and hardware
Proprietary file formats and protocols
Proprietary software often stores some of its data in file formats which are incompatible with other software, and may also communicate using protocols which are incompatible. Such formats and protocols may be restricted as trade secrets or subject to patents.
Proprietary APIs
A proprietary application programming interface (API) is a software library interface "specific to one device or, more likely to a number of devices within a particular manufacturer's product range."[32] The motivation for using a proprietary API can be vendor lock-in or because standard APIs do not support the device's functionality.[32]
The European Commission, in its March 24, 2004 decision on Microsoft's business practices,[33] quotes, in paragraph 463, Microsoft general manager for C++ development Aaron Contorer as stating in a February 21, 1997 internal Microsoft memo drafted for Bill Gates:
- TheWindows APIis so broad, so deep, and so functional that most ISVs would be crazy not to use it. And it is so deeply embedded in the source code of many Windows apps that there is a huge switching cost to using a different operating system instead.
Early versions of the iPhone SDK were covered by a non-disclosure agreement. The agreement forbade independent developers from discussing the content of the interfaces. Apple discontinued the NDA in October 2008.[34]
Vendor lock-in
Any dependency on the future versions and upgrades for a proprietary software package can create vendor lock-in, entrenching a monopoly position.[35]
Software limited to certain hardware configurations
Proprietary software may also have licensing terms that limit the usage of that software to a specific set of hardware. Apple has such a licensing model for macOS, an operating system which is limited to Apple hardware, both by licensing and various design decisions. This licensing model has been affirmed by the United States Court of Appeals.[36]
Abandonment by owners
Proprietary software which is no longer marketed, supported or sold by its owner is called abandonware, the digital form of orphaned works. If the proprietor of a software package should cease to exist, or decide to cease or limit production or support for a proprietary software package, recipients and users of the package may have no recourse if problems are found with the software. Proprietors can fail to improve and support software because of business problems.[37] Support for older or existing versions of a software package may be ended to force users to upgrade and pay for newer versions[38] (planned obsolescence). Sometimes another vendor or a software's community themselves can provide support for the software, or the users can migrate to either competing systems with longer support life cycles or to FOSS-based systems.[39]
Some closed-source software is released by their owner at end-of-life as open-source or source available software, often to prevent the software from becoming unsupported and unavailable abandonware.[40][41][42] 3D Realms and id Software are famous for the practice of releasing closed source software into the open source. Some of those kinds are free-of-charge downloads (freeware), some are still commercially sold (e.g. Arx Fatalis). More examples of formerly closed-source software in the List of commercial software with available source code and List of commercial video games with available source code.
Formerly open-source software
Some formerly open-source software was made proprietary later. Sometimes for commercialization reasons, sometimes as security or anti-cheat measurement (Security through obscurity). A famous example of such is the Doom source port ZDaemon which was prone to aimbot cheaters.[43]
Pricing and economics
Proprietary software is not synonymous with commercial software,[44][45] although the two terms are sometimes used synonymously in articles about free software.[46][47] Proprietary software can be distributed at no cost or for a fee, and free software can be distributed at no cost or for a fee.[48] The difference is that whether or not proprietary software can be distributed, and what the fee would be, is at the proprietor's discretion. With free software, anyone who has a copy can decide whether, and how much, to charge for a copy or related services.[49]
Proprietary software that comes for no cost is called freeware.
Proponents of commercial proprietary software argue that requiring users to pay for software as a product increases funding or time available for the research and development of software. For example, Microsoft says that per-copy fees maximise the profitability of software development.[50]
Proprietary software generally creates greater commercial activity over free software, especially in regard to market revenues.[51]
Examples
Examples of proprietary software include Microsoft Windows, Adobe Flash Player, PS3 OS, iTunes, Adobe Photoshop, Google Earth, macOS (formerly Mac OS X and OS X), Skype, WinRAR, Oracle's version of Java and some versions of Unix.
Software distributions considered as proprietary may in fact incorporate a "mixed source" model including both free and non-free software in the same distribution.[52] Most if not all so-called proprietary UNIX distributions are mixed source software, bundling open-source components like BIND, Sendmail, X Window System, DHCP, and others along with a purely proprietary kernel and system utilities.[53][54]
Some free software packages are also simultaneously available under proprietary terms. Examples include MySQL, Sendmail and ssh. The original copyright holders for a work of free software, even copyleft free software, can use dual-licensing to allow themselves or others to redistribute proprietary versions. Non-copyleft free software (i.e. software distributed under a permissive free software license or released to the public domain) allows anyone to make proprietary redistributions.[55][56] Free software that depends on proprietary software is considered "trapped" by the Free Software Foundation. This includes software written only for Microsoft Windows,[57] or software that could only run on Java, before it became free software.[58]
In India, one and a half million laptops were pre-loaded with screen savers of political minister Mulayam Singh Yadav. The author of software developed for these laptops included a malicious feature that would "crash" the device if the laptop's owner attempted to change, remove, or modify this feature.[59]
See also
Business software
Commercial off-the-shelf
Comparison of open-source and closed-source software
List of proprietary software for Linux
Proprietary hardware
Retail software